OIDC Adapter
What are OAuth 2.0 and OIDC?#
The OAuth 2.0 is an open authorization framework that provides for third-party applications to obtain limited access to HTTP services. The framework supports applications negotiating access directly or on behalf of a resource owner. OAuth 2.0 focuses on client developer simplicity and informs specific proven authorization flows for web, desktop and mobile applications.
OIDC is a built-upon extension of OAuth 2.0 to provide an identity layer. It enables client applications to confirm a user identity from a designated authorization server.
KivaProtocol + OIDC#
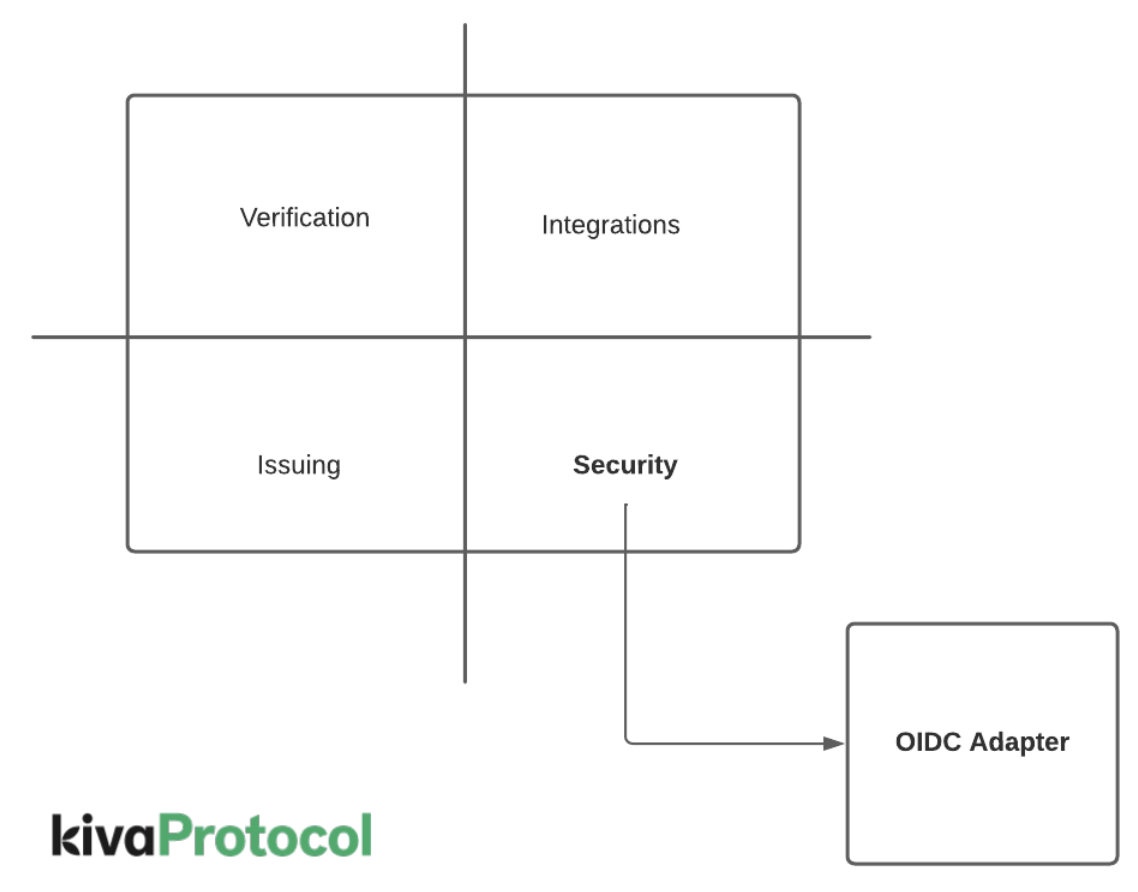
KivaProtocol architecture recognizes OAuth 2.0 + OIDC as an open standard with wide industry adoption and good vendor support. As a result, every end-user facing application built with KivaProtocol SDKs is secured by this standard.
Stack Components#
KP-Hub: Web portal to regulate access to dedicated web-based credential verification flows. In order to use the application the end user must successfully complete an OIDC interaction, this access is then passed into the verification flows.
KP-DesktopTool: Windows based application that provides a bridge between biometric sensors and web-based applications. In order to use the application the end user must successfully complete an OIDC interaction.
KP-Gateway: HTTP API that serves as a broker between client web applications, Hyperledger wallets and underlying sources of identity (eg: civil registry)
Configuring the OIDC Adapter#
To configure your instance of KivaProtocol you first need to ensure that you have a working OIDC stack. For this, you should confirm an URL of the form:
Accessing it should yield a JSON document similar to:
Checklist for Security Owner#
The owner of the authorization server and the KivaProtocol integrator must review and confirm the configuration of the following checklist:
- Client-Id for each of the end user applications connecting.
- Callback URI for each of the end user applications.